The 'Dark Skippy' Method Can Steal Private Keys from Bitcoin Hardware Wallets
Security researchers have discovered a concerning method that hackers can use to extract private keys from Bitcoin hardware wallets using just two signed transactions, dubbed "Dark Skippy." The vulnerability can affect all hardware wallet models, but only works if an attacker tricks the victim into downloading malicious firmware. A previous version of this method required victims to send "dozens" of transactions to the blockchain. However, the new "Dark Skippy" version can be

Security researchers have discovered a concerning method that hackers can use to extract private keys from Bitcoin hardware wallets using just two signed transactions, dubbed "Dark Skippy."
The vulnerability can affect all hardware wallet models, but only works if an attacker tricks the victim into downloading malicious firmware.
A previous version of this method required victims to send "dozens" of transactions to the blockchain. However, the new "Dark Skippy" version can be executed even if the victim only sends a few transactions to the blockchain. Furthermore, the attack can be carried out even when the user generates their seed phrase on a separate device.
The disclosure report was published by Lloyd Fournier, Nick Farrow, and Robin Linus on August 5. Fournier and Farrow are co-founders of hardware wallet manufacturer Frostsnap, while Linus is one of the developers behind the Bitcoin protocols ZeroSync and BitVM.
Source: Nick Farrow
According to the report, hardware wallet firmware can be programmed to embed portions of a user's seed phrase into "low-entropy secret nonces," which are then used to sign transactions. The resulting signatures are posted to the blockchain when transactions are confirmed. An attacker can scan the blockchain to find and record these signatures.
The resulting signatures only contain "public nonces," not portions of the seed phrase itself. However, an attacker can feed these public nonces into Pollard's Kangaroo Algorithm to successfully compute the secret nonces from their public counterparts.
Pollard's Kangaroo Algorithm, discovered by mathematician John Pollard, is an algorithm in computational algebra that can be used to solve the discrete logarithm problem.
According to the researchers, a user's complete seed phrase can be derived using this method, even if the user has only generated two signatures from their compromised device and even if the seed phrase was created on a separate device.
Related: Major Wallet Vulnerability Disclosed as User Recovers Only 9 BTC
Earlier versions of this vulnerability have been documented in the past. However, older versions relied on "nonce grinding," a significantly slower process that requires more transactions to be posted to the blockchain. That said, the researchers do not characterize Dark Skippy as a new vulnerability, but rather describe it as "a new way to exploit an existing vulnerability."
To mitigate the risk, the report suggests that hardware wallet manufacturers should be more diligent about preventing malicious firmware from reaching users' devices — achievable through features such as "secure boot and locked JTAG/SWD interfaces […] reproducible firmware builds signed by the vendor […], [and] other security features." Additionally, it suggests that wallet owners may want to take steps to keep their devices physically secure, including using "secret locations, personal safes, or even tamper-evident bags," though the report also acknowledges that such measures can be "inconvenient."
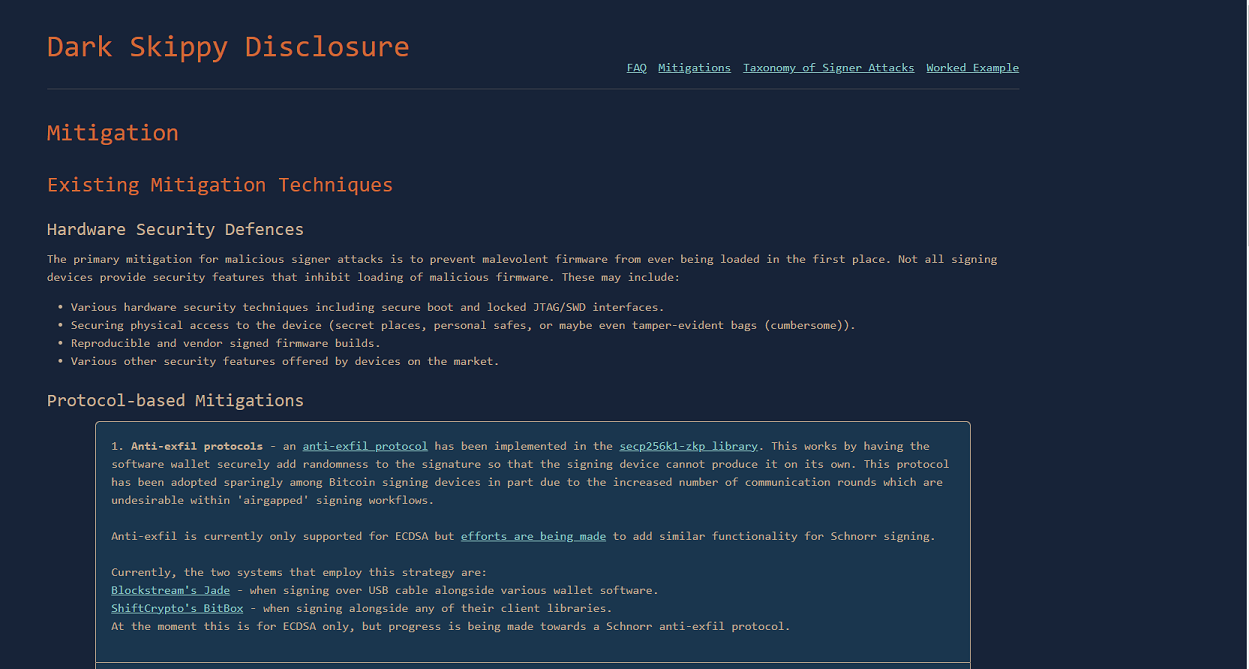
Dark Skippy mitigation techniques. Source: Dark Skippy Researchers.
Another recommendation is that wallet software should use "anti-exfiltration" signing protocols, which prevent the hardware wallet from generating nonces on its own.
Vulnerabilities in Bitcoin wallets have caused significant losses for users in the past. In August 2023, cybersecurity firm SlowMist reported that over $900,000 worth of Bitcoin was stolen through a bug in the Libbitcoin explorer library. In November, Unciphered reported that $2.1 billion in Bitcoin held in older wallets could be at risk due to a bug in the BitcoinJS wallet software.